Hackers Using Fake Trump's Scandal Video To Spread QNode Malware
Cybesecurity researchers today revealed a new malspam campaign that distributes a remote access Trojan (RAT) by purporting to contain a sex scandal video of U.S. President Donald Trump.
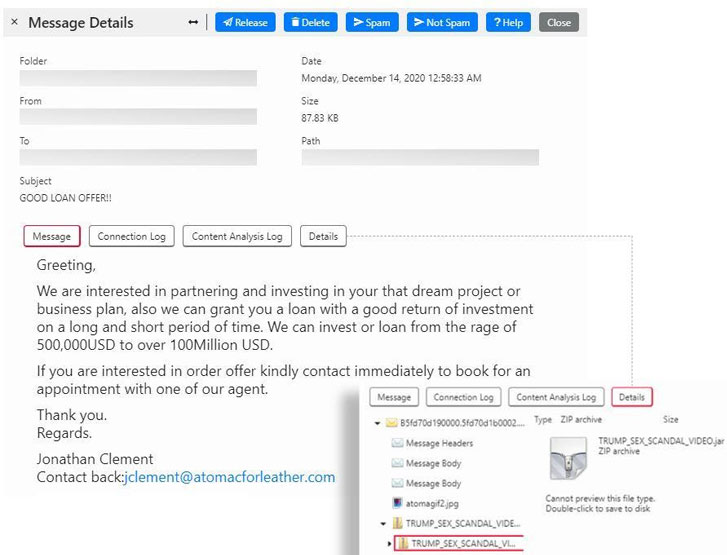
The emails, which carry with the subject line "GOOD LOAN OFFER!!," come attached with a Java archive (JAR) file called "TRUMP_SEX_SCANDAL_VIDEO.jar," which, when downloaded, installs Qua or Quaverse RAT (QRAT) onto the infiltrated system.
"We suspect that the bad guys are attempting to ride the frenzy brought about by the recently concluded Presidential elections since the filename they used on the attachment is totally unrelated to the email's theme," Trustwave's Senior Security Researcher Diana Lopera said in a write-up published today.
The latest campaign is a variant of the Windows-based QRAT downloader Trustwave researchers discovered in August.
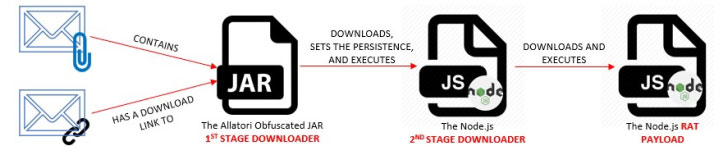
The infection chain starts with a spam message containing an embedded attachment or a link pointing to a malicious zip file, either of which retrieves a JAR file ("Spec#0034.jar") that's scrambled using the Allatori Java obfuscator.
This first stage downloader sets up the Node.Js platform onto the system and then downloads and executes a second-stage downloader called "wizard.js" that's responsible for achieving persistence and fetching and running the Qnode RAT ("qnode-win32-ia32.js") from an attacker-controlled server.
QRAT is a typical remote access Trojan with various features including, obtaining system information, performing file operations, and acquiring credentials from applications such as Google Chrome, Firefox, Thunderbird, and Microsoft Outlook.
What's changed this time around is the inclusion of a new pop-up alert that informs the victim that the JAR being run is a remote access software used for penetration testing. This also means the sample's malicious behavior only begins to manifest once the user clicks the "Ok, I know what I am doing." button.
"This pop-up is a little odd and is perhaps an attempt to make the application look legitimate, or deflect responsibility from the original software authors," Lopera noted.
Furthermore, the malicious code of the JAR downloader is split-up into different randomly-numbered buffers in an attempt to evade detection.
Other changes include an overall increase in the JAR file size and the elimination of the second-stage downloader in favor of an updated malware chain that immediately fetches the QRAT payload now called "boot.js."
For its part, the RAT has received its own share of updates, with the code now encrypted with base64 encoding, in addition to taking charge of persisting on the target system via a VBS script.
"This threat has been significantly enhanced over the past few months since we first examined it," Topera concluded, urging administrators to block the incoming JARs in their email security gateways.
"While the attachment payload has some improvements over previous versions, the email campaign itself was rather amateurish, and we believe that the chance this threat will be delivered successfully is higher if only the email was more sophisticated."
Source: feedproxy.google.com
 Reviewed by Anonymous
on
6:07 AM
Rating:
Reviewed by Anonymous
on
6:07 AM
Rating: