Hackers Backdoor Unpatched Microsoft SQL Database Servers With Cobalt Strike
Vulnerable internet-facing Microsoft SQL (MS SQL) Servers are being targeted by threat actors as part of a new campaign to deploy the Cobalt Strike adversary simulation tool on compromised hosts.
"Attacks that target MS SQL servers include attacks to the environment where its vulnerability has not been patched, brute forcing, and dictionary attack against poorly managed servers," South Korean cybersecurity company AhnLab Security Emergency Response Center (ASEC) said in a report published Monday.
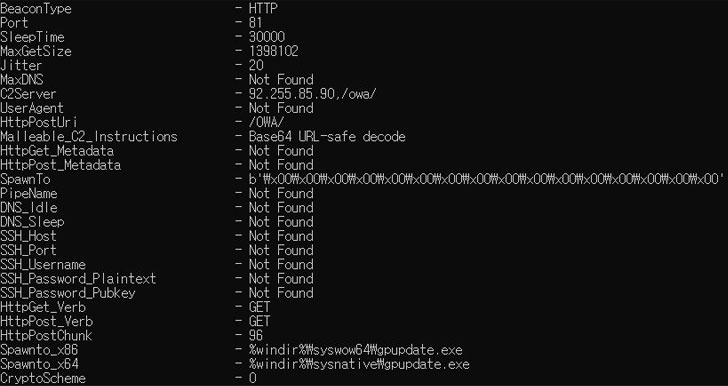
Cobalt Strike is a commercial, full-featured penetration testing framework that allows an attacker to deploy an agent named "Beacon" on the victim machine, granting the operator remote access to the system. Although billed as a red team threat simulation platform, cracked versions of the software have been actively used by a wide range of threat actors.
Intrusions observed by ASEC involve the unidentified actor scanning port 1433 to check for exposed MS SQL servers to perform brute force or dictionary attacks against the system administrator account, i.e., "sa" account, to attempt a log in.
That's not to say that servers not left accessible over the internet aren't vulnerable, what with the threat actor behind LemonDuck malware scanning the same port to laterally move across the network.
"Managing admin account credentials so that they're vulnerable to brute forcing and dictionary attacks as above or failing to change the credentials periodically may make the MS-SQL server the main target of attackers," the researchers said.
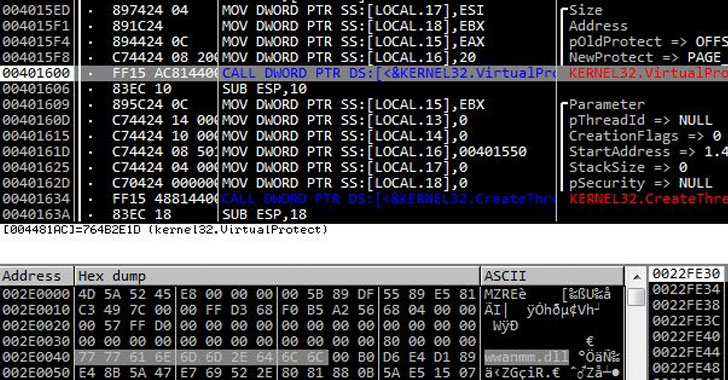
Upon successfully gaining a foothold, the next phase of the attack works by spawning a Windows command shell via the MS SQL "sqlservr.exe" process to download the next-stage payload that houses the encoded Cobalt Strike binary on to the system.
The attacks ultimately culminate with the malware decoding the Cobalt Strike executable, followed by injecting it into the legitimate Microsoft Build Engine (MSBuild) process, which has been previously abused by malicious actors to filelessly deliver remote access trojans and password-stealing malware on targeted Windows systems.
Furthermore, the Cobalt Strike that's executed in MSBuild.exe comes with additional configurations to evade detection of security software. It achieves this by loading "wwanmm.dll," a Windows library for WWan Media Manager, then writing and running the Beacon in the memory area of the DLL.
"As the beacon that receives the attacker's command and performs the malicious behavior does not exist in a suspicious memory area and instead operates in the normal module wwanmm.dll, it can bypass memory-based detection," the researchers noted.
Source: thehackernews.com
 Reviewed by Anonymous
on
11:25 PM
Rating:
Reviewed by Anonymous
on
11:25 PM
Rating: