UpdateAgent Returns With New macOS Malware Dropper Written In Swift
A new variant of the macOS malware tracked as UpdateAgent has been spotted in the wild, indicating ongoing attempts on the part of its authors to upgrade its functionalities.
"Perhaps one of the most identifiable features of the malware is that it relies on the AWS infrastructure to host its various payloads and perform its infection status updates to the server," researchers from Jamf Threat Labs said in a report.
UpdateAgent, first detected in late 2020, has since evolved into a malware dropper, facilitating the distribution of second-stage payloads such as adware while also bypassing macOS Gatekeeper protections.
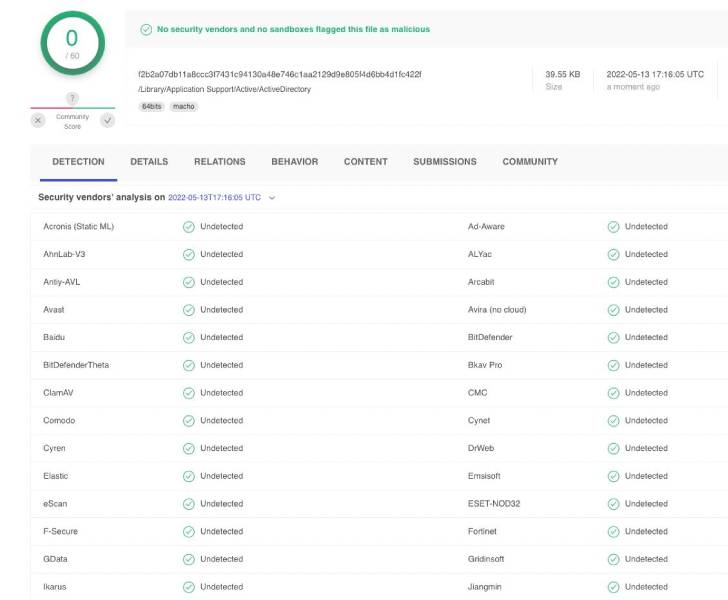
The newly discovered Swift-based dropper masquerades as Mach-O binaries named "PDFCreator" and "ActiveDirectory" that, upon execution, establish a connection to a remote server and retrieve a bash script to be executed.
"The primary difference [between the two executables] is that it reaches out to a different URL from which it should load a bash script," the researchers noted.
These bash scripts, named "activedirec.sh" or "bash_qolveevgclr.sh", include a URL pointing to Amazon S3 buckets to download and run a second-stage disk image (DMG) file to the compromised endpoint.
"The continued development of this malware shows that its authors continue to remain active, trying to reach as many users as possible," the researchers said.
Source: thehackernews.com
 Reviewed by Zion3R
on
6:41 AM
Rating:
Reviewed by Zion3R
on
6:41 AM
Rating: