Gootkit Loader Resurfaces With Updated Tactic To Compromise Targeted Computers
The operators of the Gootkit access-as-a-service (AaaS) malware have resurfaced with updated techniques to compromise unsuspecting victims.
"In the past, Gootkit used freeware installers to mask malicious files; now it uses legal documents to trick users into downloading these files," Trend Micro researchers Buddy Tancio and Jed Valderama said in a write-up last week.
The findings build on a previous report from eSentire, which disclosed in January of widespread attacks aimed at employees of accounting and law firms to deploy malware on infected systems.
Gootkit is part of the proliferating underground ecosystem of access brokers, who are known to provide other malicious actors a pathway into corporate networks for a price, paving the way for actual damaging attacks such as ransomware.
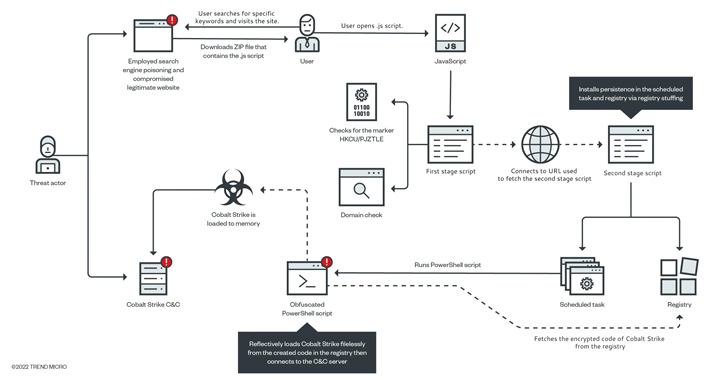
The loader utilizes malicious search engine results, a technique called SEO poisoning, to lure unsuspecting users into visiting compromised websites hosting malware-laced ZIP package files purportedly related to disclosure agreements for real estate transactions.
"The combination of SEO poisoning and compromised legitimate websites can mask indicators of malicious activity that would usually keep users on their guard," the researchers pointed out.
The ZIP file, for its part, includes a JavaScript file that loads a Cobalt Strike binary, a tool used for post-exploitation activities that run directly in the memory filelessly.
"Gootkit is still active and improving its techniques," the researchers said. "This implies that this operation has proven effective, as other threat actors seem to continue using it."
Source: thehackernews.com
 Reviewed by Zion3R
on
10:14 PM
Rating:
Reviewed by Zion3R
on
10:14 PM
Rating: