Mirai Botnet Hits Wynncraft Minecraft Server With 2.5 Tbps DDoS Attack
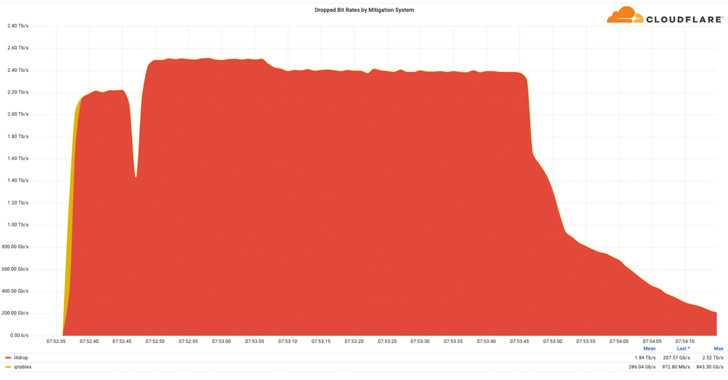
Web infrastructure and security company Cloudflare disclosed this week that it halted a 2.5 Tbps distributed denial-of-service (DDoS) attack launched by a Mirai botnet.
Characterizing it as a "multi-vector attack consisting of UDP and TCP floods," researcher Omer Yoachimik said the DDoS attack targeted the Minecraft server Wynncraft in Q3 2022.
"The entire 2.5 Tbps attack lasted about 2 minutes, and the peak of the 26 million rps attack [was] only 15 seconds," Yoachimik noted. "This is the largest attack we've ever seen from the bitrate perspective."
Cloudflare also pointed to a surge in multi-terabit DDoS attacks as well as longer-lasting volumetric attacks during the time period, not to mention an uptick in attacks targeting Taiwan and Japan.
The disclosure comes almost 10 months after Microsoft said it thwarted a record-breaking 3.47 Tbps DDoS attack in November 2021 directed against an unnamed Azure customer in Asia.
Other DDoS attacks of this scale and volume include a 2.5 Tbps DDoS attack absorbed by Google in September 2017 and a 2.3 Tbps volumetric strike aimed at Amazon Web Services in February 2020.
What's more, ransom DDoS attacks – in which the threat actor demands monetary compensation to stop the attack – have witnessed a 15% increase quarter-over-quarter and a 67% jump year-over-year.
Application-layer DDoS attacks (aka HTTP DDoS attacks), on the other hand, have singled out companies in the U.S., China, and Cyprus, with most of the attacks originating from China, India, and the U.S.
Ukraine, which has been heavily pummeled by DDoS attacks since the start of the Russo-Ukrainian war, has had its marketing, education, and government sectors targeted the most during Q3, in contrast to attacks on media companies the previous two quarters.
Likewise, network-layer DDoS attacks (aka Layer 3 DDoS attacks) predominantly were recorded against gaming, telecom, IT services sectors located in Singapore, U.S., and China.
A noteworthy trend highlighted by Cloudflare is a 1,221% QoQ increase in DDoS attacks that leverage the BitTorrent communication protocol, which is traditionally used for peer-to-peer (P2P) file sharing.
"Over the years, it has become easier, cheaper, and more accessible for attackers and attackers-for-hire to launch DDoS attacks," Yoachimik said.
The disclosure also comes as application performance management company Netscout revealed that threat actors are experimenting with different DDoS attack vectors such as carpet bombing and DNS water torture attacks.
Source: thehackernews.com
 Reviewed by Zion3R
on
12:23 AM
Rating:
Reviewed by Zion3R
on
12:23 AM
Rating: