Mitigation For Exchange Zero-Days Bypassed! Microsoft Issues New Workarounds
Microsoft has revised its mitigation measures for the newly disclosed and actively exploited zero-day flaws in Exchange Server after it was found that they could be trivially bypassed.
The two vulnerabilities, tracked as CVE-2022-41040 and CVE-2022-41082, have been codenamed ProxyNotShell due to similarities to another set of flaws called ProxyShell, which the tech giant resolved last year.
In-the-wild attacks abusing the shortcomings have chained the two flaws to gain remote code execution on compromised servers with elevated privileges, leading to the deployment of web shells.
The Windows maker, which is yet to release a fix for the bugs, has acknowledged that a single state-sponsored threat actor may have been weaponizing the flaws since August 2022 in limited targeted attacks.
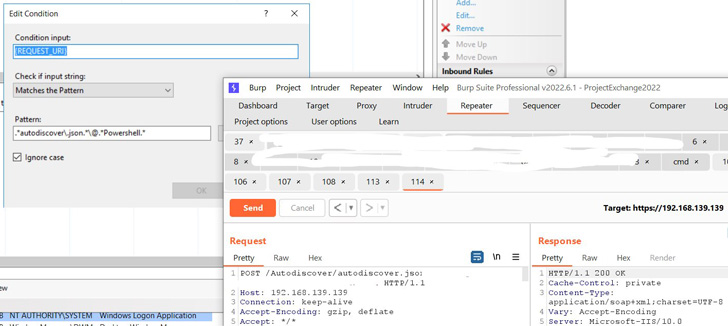
To reduce the risk of exploitation, the company also shared temporary workarounds that are designed to restrict known attack patterns through a rule in the IIS Manager.
However, according to security researcher Jang (@testanull), the URL pattern can be easily circumvented, with senior vulnerability analyst Will Dormann noting that the block mitigations are "unnecessarily precise, and therefore insufficient."
Microsoft has since revised the URL Rewrite rule (also available as a standalone PowerShell script) to take this into account -
- Open IIS Manager
- Select Default Web Site
- In the Feature View, click URL Rewrite
- In the Actions pane on the right-hand side, click Add Rule(s)…
- Select Request Blocking and click OK
- Add the string ".*autodiscover\.json.*Powershell.*" (excluding quotes)
- Select Regular Expression under Using
- Select Abort Request under How to block and then click OK
- Expand the rule and select the rule with the pattern: .*autodiscover\.json.*Powershell.* and click Edit under Conditions
- Change the Condition input from {URL} to {REQUEST_URI}
It's not immediately clear when Microsoft plans to push a patch for the two vulnerabilities, but it's possible that they could be shipped as part of Patch Tuesday updates next week on October 11, 2022.
Source: thehackernews.com
 Reviewed by Zion3R
on
11:10 PM
Rating:
Reviewed by Zion3R
on
11:10 PM
Rating: