These Two Google Play Store Apps Spotted Distributing Xenomorph Banking Trojan
Google has removed two new malicious dropper apps that have been detected on the Play Store for Android, one of which posed as a lifestyle app and was caught distributing the Xenomorph banking malware.
"Xenomorph is a trojan that steals credentials from banking applications on users' devices," Zscaler ThreatLabz researchers Himanshu Sharma and Viral Gandhi said in an analysis published Thursday.
"It is also capable of intercepting users' SMS messages and notifications, enabling it to steal one-time passwords and multi-factor authentication requests."
The cybersecurity firm said it also found an expense tracker app that exhibited similar behavior, but noted that it couldn't extract the URL used to fetch the malware artifact.
The two malicious apps are as follows -
- Todo: Day manager (com.todo.daymanager)
- 経費キーパー (com.setprice.expenses)
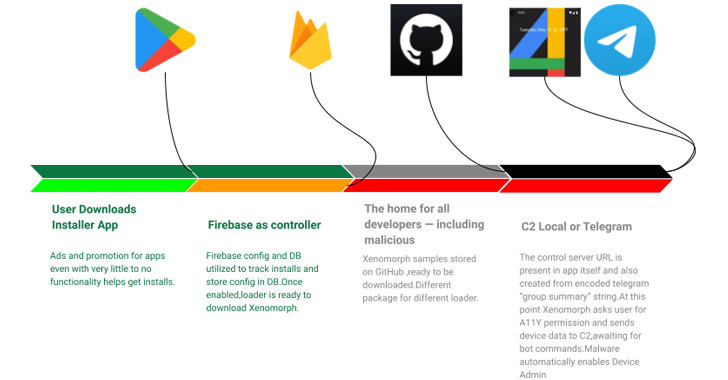
Both the apps function as a dropper, meaning the apps themselves are harmless and are a conduit to retrieve the actual payload, which, in the case of Todo, is hosted on GitHub.
Xenomorph, first documented by ThreatFabric earlier this February, is known to abuse Android's accessibility permissions to conduct overlay attacks, wherein fake login screens are presented atop legitimate bank apps to steal victim's credentials.
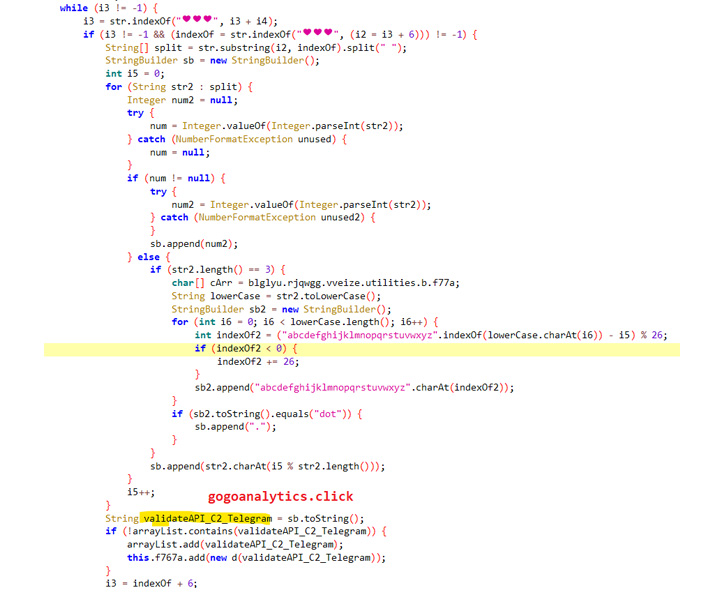
What's more, the malware leverages a Telegram channel's description to decode and construct the command-and-control (C2) domain used to receive additional commands.
The development follows the discovery of four rogue apps on Google Play that were found directing victims to malicious websites as part of an adware and information-stealing campaign. Google told The Hacker News that it has since banned the developer.
Source: thehackernews.com
 Reviewed by Zion3R
on
5:32 AM
Rating:
Reviewed by Zion3R
on
5:32 AM
Rating: