Hackers Exploiting Redis Vulnerability To Deploy New Redigo Malware On Servers
A previously undocumented Go-based malware is targeting Redis servers with the goal of taking control of the infected systems and likely building a botnet network.
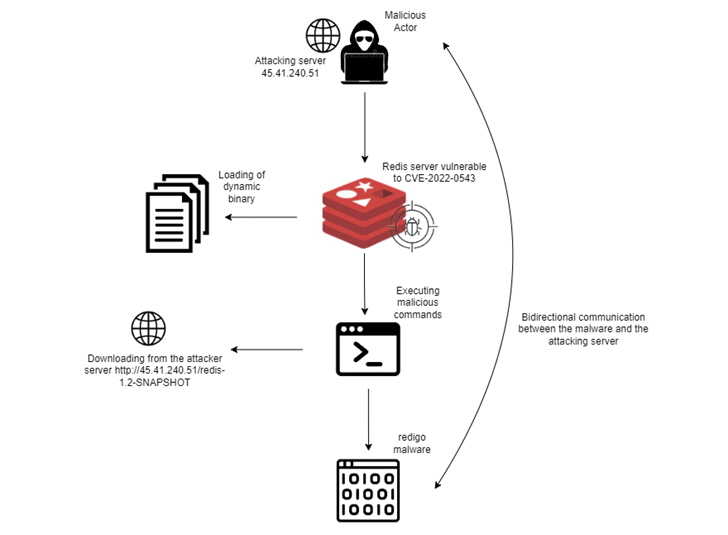
The attacks involve taking advantage of a critical security vulnerability in the open source, in-memory, key-value store that was disclosed earlier this year to deploy Redigo, according to cloud security firm Aqua.
Tracked as CVE-2022-0543 (CVSS score: 10.0), the weakness pertains to a case of sandbox escape in the Lua scripting engine that could be leveraged to attain remote code execution.
This is not the first time the flaw has come under active exploitation, what with Juniper Threat Labs uncovering attacks perpetrated by the Muhstik botnet in March 2022 to execute arbitrary commands.
The Redigo infection chain is similar in that the adversaries scan for exposed Redis servers on port 6379 to establish initial access, following it up by downloading a shared library "exp_lin.so" from a remote server.
This library file comes with an exploit for CVE-2022-0543 to execute a command in order to retrieve Redigo from the same server, in addition to taking steps to mask its activity by simulating legitimate Redis cluster communication over port 6379.
"The dropped malware mimics the Redis server communication which allowed the adversaries to hide communications between the targeted host and the C2 server," Aqua researcher Nitzan Yaakov explained.
It's not known what the end goal of the attacks are, but it's suspected that the compromised hosts could be co-opted into a botnet to facilitate DDoS attacks or used to steal sensitive information from the database server to further extend their reach.
Source: thehackernews.com
 Reviewed by Zion3R
on
11:38 AM
Rating:
Reviewed by Zion3R
on
11:38 AM
Rating: