Cacti Servers Under Attack As Majority Fail To Patch Critical Vulnerability
A majority of internet-exposed Cacti servers have not been patched against a recently patched critical security vulnerability that has come under active exploitation in the wild.
That's according to attack surface management platform Censys, which found only 26 out of a total of 6,427 servers to be running a patched version of Cacti (1.2.23 and 1.3.0).
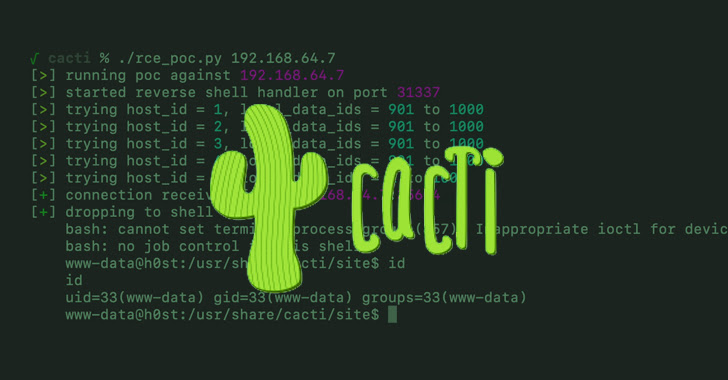
The issue in question relates to CVE-2022-46169 (CVSS score: 9.8), a combination of authentication bypass and command injection that enables an unauthenticated user to execute arbitrary code on an affected version of the open-source, web-based monitoring solution.
Details about the flaw, which impacts versions 1.2.22 and below, were first revealed by SonarSource. The flaw was reported to the project maintainers on December 2, 2022.
"A hostname-based authorization check is not implemented safely for most installations of Cacti," SonarSource researcher Stefan Schiller noted earlier this month, adding "unsanitized user input is propagated to a string used to execute an external command."
The public disclosure of the vulnerability has also led to "exploitation attempts," with the Shadowserver Foundation and GreyNoise warning of malicious attacks originating from one IP address located in Ukraine so far.
A majority of the unpatched versions (1,320) are located in Brazil, followed by Indonesia, the U.S., China, Bangladesh, Russia, Ukraine, the Philippines, Thailand, and the U.K.
SugarCRM Flaw Actively Exploited to Drop Web Shells
The development comes as SugarCRM shipped fixes for a publicly disclosed vulnerability that has also been actively weaponized to drop a PHP-based web shell on 354 unique hosts, Censys said in an independent advisory.
The bug, tracked as CVE-2023-22952, concerns a case of missing input validation that could result in injection of arbitrary PHP code. It has been addressed in SugarCRM versions 11.0.5 and 12.0.2.
In the attacks detailed by Censys, the web shell is used as a conduit to execute additional commands on the infected machine with the same permissions as the user running the web service. A majority of the infections have been reported in the U.S., Germany, Australia, France, and the U.K.
It's not uncommon for malicious actors to capitalize on newly disclosed vulnerabilities to carry out their attacks, making it imperative that users move quickly plug the security holes.
Source: thehackernews.com
 Reviewed by Zion3R
on
12:35 AM
Rating:
Reviewed by Zion3R
on
12:35 AM
Rating: