Chinese Hackers Targeting South American Diplomatic Entities With ShadowPad
Microsoft on Monday attributed a China-based cyber espionage actor to a set of attacks targeting diplomatic entities in South America.
The tech giant's Security Intelligence team is tracking the cluster under the emerging moniker DEV-0147, describing the activity as an "expansion of the group's data exfiltration operations that traditionally targeted government agencies and think tanks in Asia and Europe."
The threat actor is said to use established hacking tools such as ShadowPad to infiltrate targets and maintain persistent access.
ShadowPad, also called PoisonPlug, is a successor to the PlugX remote access trojan and has been widely put to use by Chinese adversarial collectives with links to the Ministry of State Security (MSS) and People's Liberation Army (PLA), per Secureworks.
One of the other malicious payloads put to use by DEV-0147 is a webpack loader called QuasarLoader, which allows for deploying additional payloads onto the compromised hosts.
Redmond did not disclose the method DEV-0147 might be using to gain initial access to a target environment. That said, phishing and opportunistic targeting of unpatched applications are likely vectors.
"DEV-0147's attacks in South America included post-exploitation activity involving the abuse of on-premises identity infrastructure for recon and lateral movement, and the use of Cobalt Strike for command-and-control and data exfiltration," Microsoft said.
DEV-0147 is far from the only China-based advanced persistent threat (APT) to leverage ShadowPad in recent months.
In September 2022, NCC Group unearthed details of an attack aimed at an unnamed organization that leveraged a critical flaw in WSO2 (CVE-2022-29464, CVSS score: 9.8) to drop web shells and activate an infection chain that led to the delivery of ShadowPad for intelligence gathering.
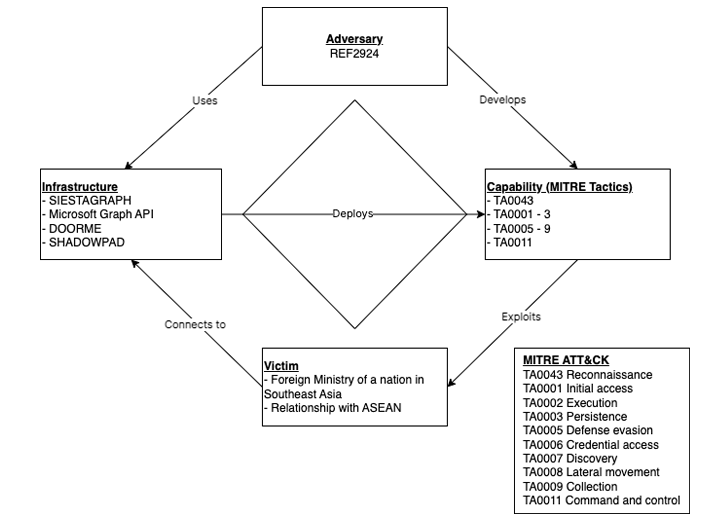
ShadowPad has also been employed by unidentified threat actors in an attack targeting an ASEAN member foreign ministry through the successful exploitation of a vulnerable, and Internet-connected, Microsoft Exchange Server.
The activity, dubbed REF2924 by Elastic Security Labs, has been observed to share tactical associations with those adopted by other nation-state groups such as Winnti (aka APT41) and ChamelGang.
"The REF2924 intrusion set [...] represents an attack group that appears focused on priorities that, when observed across campaigns, align with a sponsored national strategic interest," the company noted.
The fact that Chinese hacking groups continue to use ShadowPad despite it being well-documented over the years suggests the technique is yielding some success.
Source: thehackernews.com
 Reviewed by Zion3R
on
2:28 AM
Rating:
Reviewed by Zion3R
on
2:28 AM
Rating: