Cybercriminals Renting WikiLoader To Target Italian Organizations With Banking Trojan
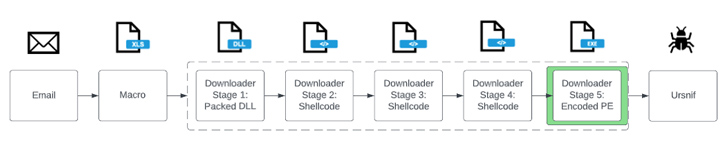
Organizations in Italy are the target of a new phishing campaign that leverages a new strain of malware called WikiLoader with an ultimate aim to install a banking trojan, stealer, and spyware called Ursnif (aka Gozi).
"It is a sophisticated downloader with the objective of installing a second malware payload," Proofpoint said in a technical report. "The malware uses multiple mechanisms to evade detection and was likely developed as a malware that can be rented out to select cybercriminal threat actors."
WikiLoader is so named due to the malware making a request to Wikipedia and checking that the response has the string "The Free."
The enterprise security firm said it first detected the malware in the wild on December 27, 2022, in connection with an intrusion set mounted by a threat actor it tracks as TA544, which is also known as Bamboo Spider and Zeus Panda.
The campaigns are centered around the use of emails containing either Microsoft Excel, Microsoft OneNote, or PDF attachments that act as a lure to deploy the downloader, which is subsequently used to install Ursnif.
In a sign that WikiLoader is shared among multiple cybercrime groups, the threat actor dubbed TA551 (aka Shathak) has also been observed employing the malware as of late March 2023.
Recent TA544 campaigns detected in mid-July 2023 have utilized accounting themes to propagate PDF attachments with URLs that, when clicked, lead to the delivery of a ZIP archive file, which, in turn, packs a JavaScript file designed to download and execute WikiLoader.
WikiLoader is heavily obfuscated and comes with evasive maneuvers to bypass endpoint security software and avoid detonation in automated analysis environments. It's also engineered to retrieve and run a shellcode payload hosted on Discord, which is ultimately used to launch Ursnif.
Worried about insider threats? We've got you covered! Join this webinar to explore practical strategies and the secrets of proactive security with SaaS Security Posture Management.
Join Today"It is currently under active development, and its authors appear to make regular changes to try and remain undetected and fly under the radar," Selena Larson, senior threat intelligence analyst at Proofpoint, said in a statement.
"It is likely more criminal threat actors will use this, especially those known as initial access brokers (IABs) that conduct regular activity that leads to ransomware. Defenders should be aware of this new malware and activities involved in payload delivery, and take steps to protect their organizations against exploitation."
Source: thehackernews.com
 Reviewed by Zion3R
on
9:40 PM
Rating:
Reviewed by Zion3R
on
9:40 PM
Rating: