Alert: Apache SuperSet Vulnerabilities Expose Servers To Remote Code Execution Attacks
Patches have been released to address two new security vulnerabilities in Apache SuperSet that could be exploited by an attacker to gain remote code execution on affected systems.
The update (version 2.1.1) plugs CVE-2023-39265 and CVE-2023-37941, which make it possible to conduct nefarious actions once a bad actor is able to gain control of Superset's metadata database.
Outside of these weaknesses, the latest version of Superset also remediates a separate improper REST API permission issue (CVE-2023-36388) that allows for low-privilege users to carry out server-side request forgery (SSRF) attacks.
"Superset by design allows privileged users to connect to arbitrary databases and execute arbitrary SQL queries against those databases using the powerful SQLLab interface," Horizon3.ai's Naveen Sunkavally said in a technical write-up.
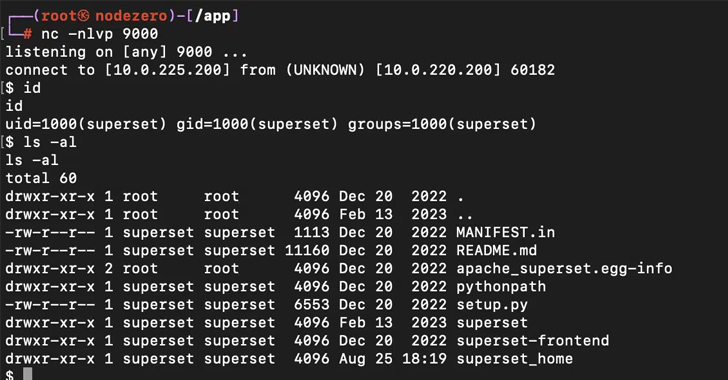
"If Superset can be tricked into connecting to its own metadata database, an attacker can directly read or write application configuration through SQLLab. This leads to harvesting credentials and remote code execution."
CVE-2023-39265 relates to a case of URI bypass when connecting to the SQLite database used for the metastore, enabling an attacker to execute data manipulation commands.

Also tracked as part of the same CVE identifier is the lack of validation when importing SQLite database connection information from a file, which could be abused to import a maliciously crafted ZIP archive file.
"Superset versions from 1.5 to 2.1.0 use python's pickle package to store certain configuration data," Sunkavally said about CVE-2023-37941.
"An attacker with write access to the metadata database can insert an arbitrary pickle payload into the store, and then trigger deserialization of it, leading to remote code execution."
Some of the other flaws that have been patched in the latest release are below -
- An MySQL arbitrary file read vulnerability that could be exploited to get credentials to the metadata database
- The abuse of superset load_examples command to get the metadata database URI from the user interface and modify data stored in it
- The use of default credentials to access the metadata database in some installations of Superset
- The leak of database credentials in plaintext when querying the /api/v1/database API as a privileged user (CVE-2023-30776, fixed in 2.1.0)
The disclosure comes a little over four months after the company disclosed a high-severity flaw in the same product (CVE-2023-27524, CVSS score: 8.9) that could enable unauthorized attackers to gain admin access to the servers and execute arbitrary code.
Achieved MFA? PAM? Service account protection? Find out how well-equipped your organization truly is against identity threats
Supercharge Your SkillsThe problem arises as a result of using a default SECRET_KEY that could be abused by attackers to authenticate and access unauthorized resources on internet-exposed installations.
Since the public disclosure of the flaw in April 2023, Horizon3.ai said 2076 out of 3842 Superset servers are still using a default SECRET_KEY, with about 72 instances using a trivially guessable SECRET_KEY like superset, SUPERSET_SECRET_KEY, 1234567890, admin, changeme, thisisasecretkey, and your_secret_key_here.
"The user is responsible for setting the Flask SECRET_KEY, which invariably leads to some users setting weak keys," Sunkavally said, urging the maintainers to add support for automatically generating the key.
"At the root of many of the vulnerabilities [...] is the fact that the Superset web interface permits users to connect to the metadata database. At the root of many of the vulnerabilities in this post is the fact that the Superset web interface permits users to connect to the metadata database."
Source: thehackernews.com
 Reviewed by Zion3R
on
4:20 AM
Rating:
Reviewed by Zion3R
on
4:20 AM
Rating: