ExelaStealer: A New Low-Cost Cybercrime Weapon Emerges
A new information stealer named ExelaStealer has become the latest entrant to an already crowded landscape filled with various off-the-shelf malware designed to capture sensitive data from compromised Windows systems.
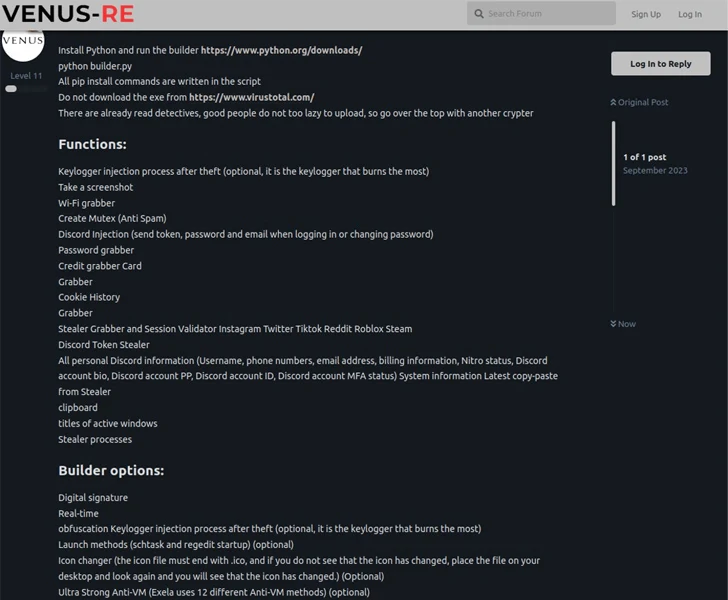
"ExelaStealer is a largely open-source infostealer with paid customizations available from the threat actor," Fortinet FortiGuard Labs researcher James Slaughter said in a technical report.
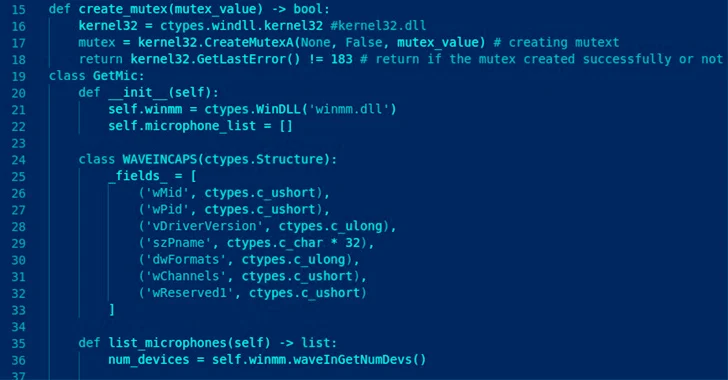
Written in Python and incorporating support for JavaScript, it comes fitted with capabilities to siphon passwords, Discord tokens, credit cards, cookies and session data, keystrokes, screenshots, and clipboard content.
ExelaStealer is offered for sale via cybercrime forums as well as a dedicated Telegram channel set up by its operators who go by the online alias quicaxd. The paid-for version costs $20 a month, $45 for three months, or $120 for a lifetime license.
The low cost of the commodity malware makes it a perfect hacking tool for newbies, effectively lowering the barrier to entry for pulling off malicious attacks.
The stealer binary, in its current form, can only be compiled and packaged on a Windows-based system using a builder Python script, which throws necessary source code obfuscation to the mix in an attempt to resist analysis.
There is evidence to suggest that ExelaStealer is being distributed via an executable that masquerades as a PDF document, indicating that the initial intrusion vector could be anything ranging from phishing to watering holes.
Launching the binary displays a lure document – a Turkish vehicle registration certificate for a Dacia Duster – while stealthily activating the stealer in the background.
"Data has become a valuable currency, and because of this, attempts to gather it will likely never cease," Slaughter said.
"Infostealer malware exfiltrates data belonging to corporations and individuals that can be used for blackmail, espionage, or ransom. Despite the number of infostealers in the wild, ExelaStealer shows there is still room for new players to emerge and gain traction."
The disclosure comes as Kaspersky revealed details of a campaign that targets government, law enforcement, and non-profit organizations to drop several scripts and executables at once to conduct cryptocurrency mining, steal data using keyloggers, and gain backdoor access to systems.
"The B2B sector remains attractive to cybercriminals, who seek to exploit its resources for money-making purposes," the Russian cybersecurity firm said, noting that most of the attacks were aimed at organizations in Russia, Saudi Arabia, Vietnam, Brazil, Romania, the U.S., India, Morocco, and Greece.
Earlier this week, U.S. cybersecurity and intelligence agencies released a joint advisory outlining the phishing techniques malicious actors commonly use to obtain login credentials and deploy malware, highlighting their attempts to impersonate a trusted source to realize their goals.
Source: thehackernews.com
 Reviewed by Zion3R
on
2:53 AM
Rating:
Reviewed by Zion3R
on
2:53 AM
Rating: